Giving users read-only access to a Amazon S3 bucket
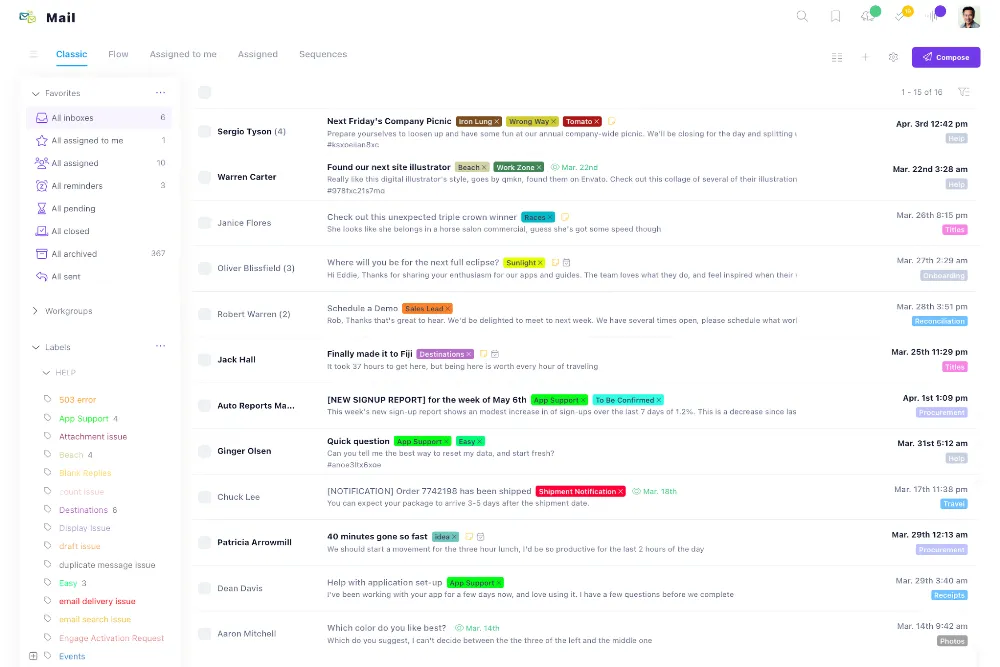
Recently I’ve had the need to give a user a read-only access to a bucket on Amazon S3. Amazon provides the IAM (Identity and Access Management) Console for this. While adding a user is easy, the trickier part is the policies you have to apply.
While Amazon applies some templates and links to the description I was still not able to provide access for my user. After fiddling around some more, I read that you need to provide “listbucket” access to any account that you want to give read-only access to a specific bucket! Duh, I wish Amazon would have simply included that in their templates.
In any case, I hope the below snippet will help someone:
[code]{
"Statement": [
{
"Effect": "Allow",
"Action": "s3:ListAllMyBuckets",
"Resource": "arn:aws:s3:::*"
},
{
"Effect": "Allow",
"Action": "s3:*",
"Resource": [
"arn:aws:s3:::BUCKET",
"arn:aws:s3:::BUCKET/*"
]
}
]
}[/code]